Protecting Distributed Systems from Disruptions
Grid computing clusters power scientific research, financial modeling, and large-scale simulations by distributing computational tasks across multiple connected nodes. While this architecture enhances efficiency and scalability, it also presents security vulnerabilities. One of the most serious threats is Distributed Denial-of-Service (DDoS) attacks, which can overwhelm grid systems, disrupt operations, and compromise resource availability.
DDoS attacks target network bandwidth, processing power, or memory by flooding a system with malicious traffic. In a grid computing environment, where multiple nodes communicate and share resources, an attack can quickly spread and bring down critical workloads. Without adequate protection, grid clusters may experience performance degradation, downtime, and potential data loss.
To safeguard grid computing clusters, organizations must implement proactive security measures. This article explores the risks of DDoS attacks, common attack methods, and effective defense strategies to ensure uninterrupted performance and reliability.
Understanding the Impact of DDoS Attacks on Grid Computing
DDoS attacks exploit the distributed nature of grid computing, making them particularly dangerous. Since grid environments rely on multiple connected systems, an attack on one node can rapidly affect others, leading to widespread service disruption.
One of the primary consequences of a DDoS attack is resource exhaustion. Attackers flood the system with artificial requests, causing computational resources to become overloaded. This prevents legitimate users from accessing services, leading to project delays and financial losses.
Additionally, DDoS attacks can serve as distractions for other malicious activities. While security teams focus on mitigating the flood of traffic, attackers may attempt data breaches, malware injections, or unauthorized system access. These secondary threats can have long-term consequences for grid computing infrastructures.
Common Types of DDoS Attacks Targeting Grid Systems
Understanding how attackers launch DDoS attacks is the first step in developing effective countermeasures. Several attack methods are commonly used against grid computing environments, each targeting different system vulnerabilities.
Volumetric attacks are among the most common. These attacks overwhelm the network by flooding it with excessive traffic, consuming bandwidth and making communication between grid nodes impossible. Examples include UDP floods and ICMP floods, which send massive amounts of data packets to exhaust network capacity.
Another method is protocol-based attacks, which exploit weaknesses in communication protocols used by grid computing clusters. SYN floods, for instance, take advantage of the TCP handshake process, leaving grid nodes stuck in a state of half-open connections, preventing them from responding to legitimate requests.
Application-layer attacks target specific services within a grid computing environment. These attacks mimic legitimate user behavior to exhaust processing power and disrupt critical applications. HTTP floods and Slowloris attacks fall into this category, making them harder to detect since they don’t rely on massive traffic volumes.
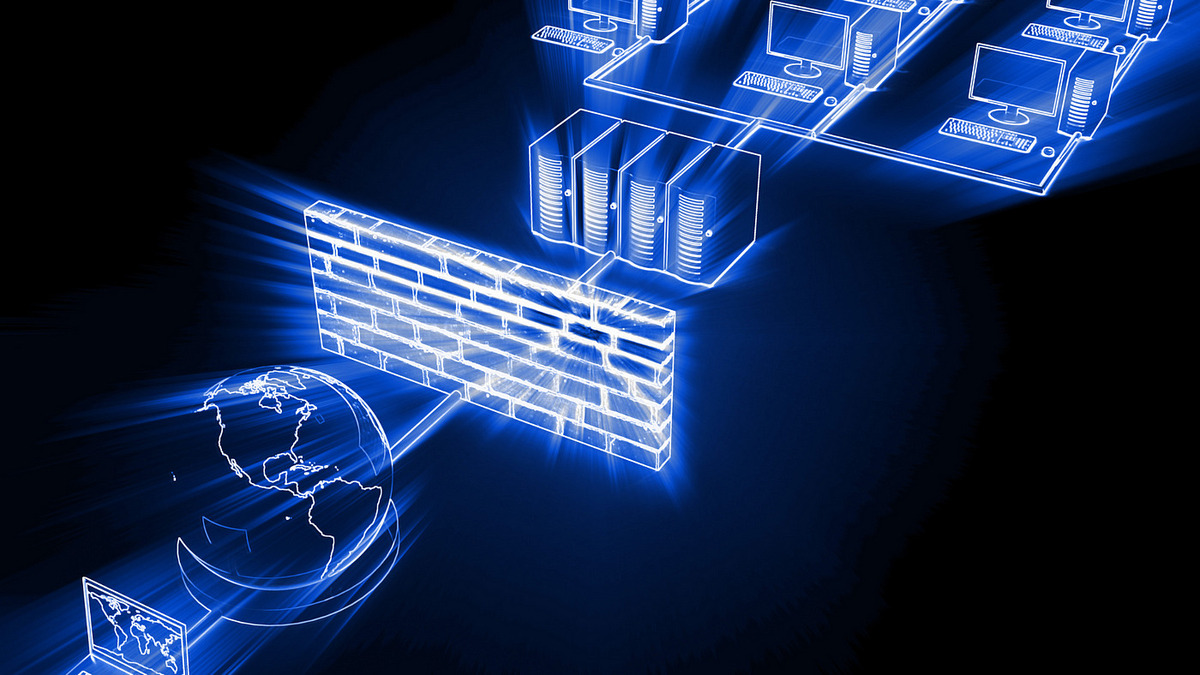
Strengthening Network Infrastructure Against DDoS Attacks
One of the most effective ways to mitigate DDoS threats is by reinforcing the network infrastructure. Implementing strong security protocols ensures that malicious traffic is filtered before reaching the grid computing environment.
Traffic filtering mechanisms, such as firewalls and intrusion prevention systems (IPS), help detect and block suspicious requests. By setting up access control lists (ACLs), organizations can restrict inbound traffic to trusted sources, reducing exposure to malicious activity.
Using rate limiting and throttling techniques can prevent excessive traffic from overwhelming grid nodes. These measures help balance network loads by setting maximum request rates, ensuring that no single user or system can monopolize resources.
Deploying DDoS Protection Services and Mitigation Tools
Specialized DDoS protection services offer an additional layer of defense by identifying and mitigating attacks before they impact grid computing clusters. Many cloud-based solutions use AI-driven threat detection to analyze traffic patterns in real-time.
Scrubbing centers are a valuable asset in DDoS mitigation. These centers divert incoming traffic through a filtering system that removes malicious packets while allowing legitimate requests to pass through. This approach helps maintain system availability during an attack.
Organizations can also deploy Web Application Firewalls (WAF) to protect application-layer services within grid environments. A WAF inspects HTTP traffic and blocks suspicious requests, reducing the risk of targeted disruptions.
Implementing Load Balancing to Reduce Attack Impact
Load balancing distributes traffic across multiple nodes, preventing any single system from becoming overwhelmed. This strategy enhances fault tolerance by ensuring that if one node is affected by an attack, others can continue operating normally.
Using distributed load balancers helps manage incoming requests dynamically, redirecting traffic based on real-time network conditions. This prevents attackers from overwhelming a single access point, making it harder for them to disrupt grid computing operations.
Incorporating redundant pathways within the network further enhances resilience. If an attack targets one route, traffic can be rerouted through alternate pathways, maintaining system functionality without service interruptions.
Leveraging AI and Machine Learning for Threat Detection
Artificial intelligence (AI) and machine learning (ML) play a critical role in identifying and mitigating DDoS threats. These technologies can analyze vast amounts of data to detect abnormal traffic patterns and predict potential attacks.
Behavioral analysis tools use machine learning algorithms to differentiate between legitimate users and attack traffic. By recognizing deviations from normal behavior, these tools can flag suspicious activity in real-time, allowing security teams to respond swiftly.
Automated response systems take AI capabilities a step further by deploying countermeasures without human intervention. If an attack is detected, AI-driven security systems can block malicious IP addresses, redirect traffic, and adjust firewall rules dynamically to mitigate damage.
Establishing Incident Response Plans for DDoS Attacks
Despite the best preventive measures, organizations must have a clear incident response plan in place. A well-prepared team can minimize downtime and mitigate potential losses when a DDoS attack occurs.
Developing a response framework includes defining roles and responsibilities for IT security personnel. Having predefined escalation procedures ensures that the right teams take immediate action when an attack is detected.
Regular security drills and attack simulations help organizations test their response plans under realistic conditions. These exercises allow teams to identify weaknesses, refine mitigation strategies, and improve overall preparedness.
Building a Resilient Grid Computing Security Strategy
Securing grid computing clusters from DDoS attacks requires a multi-layered approach that combines network defenses, load balancing, AI-driven monitoring, and incident response planning. Organizations must continuously evaluate and adapt their security strategies to counter evolving threats.
By investing in robust infrastructure, leveraging real-time threat detection, and fostering a security-aware culture, grid computing environments can maintain performance and reliability even in the face of cyber threats. Proactive security measures ensure that researchers, businesses, and institutions can continue benefiting from the immense computational power of grid systems without disruption.