Securing Distributed Computing Environments
Grid computing enables organizations to share and utilize computing resources across distributed systems, making it a powerful solution for high-performance computing. However, with increased connectivity comes significant security challenges, particularly unauthorized access. If left unchecked, unauthorized users can exploit vulnerabilities, steal sensitive data, or disrupt operations.
Security threats in grid computing are unique because of the decentralized nature of the infrastructure. Unlike traditional computing systems, grid environments involve multiple users, institutions, and networks, all of which need to interact securely. Without proper access controls, cybercriminals can compromise critical data or manipulate computing processes for malicious purposes.
Preventing unauthorized access requires a combination of robust authentication mechanisms, encryption, and continuous monitoring. Organizations must implement layered security strategies that ensure only legitimate users gain access while keeping threats at bay. This article explores essential measures to strengthen security and protect grid computing systems from unauthorized access.
Understanding the Risks of Unauthorized Access
Unauthorized access in grid computing can have severe consequences, from data breaches to compromised research integrity. Attackers may attempt to infiltrate a system for various reasons, such as stealing proprietary data, launching distributed denial-of-service (DDoS) attacks, or gaining control over computing resources for illicit activities.
One common method of unauthorized access involves exploiting weak authentication systems. If credentials are not adequately protected or multi-factor authentication is absent, attackers can gain entry using stolen or guessed passwords. Weak authentication is especially risky in grid environments where users often log in remotely from different locations.
Another significant risk comes from insider threats. Employees or researchers with legitimate access can misuse their privileges or accidentally expose the system to unauthorized entities. Implementing strict access policies and monitoring user activity can help reduce these risks and detect anomalies before they cause harm.
Implementing Strong Authentication Mechanisms
Authentication is the first line of defense against unauthorized access. A secure grid computing environment should incorporate multi-factor authentication (MFA) to ensure that users must verify their identity using multiple credentials, such as a password and a one-time verification code.
Public Key Infrastructure (PKI) is another widely used authentication method in grid computing. PKI enables secure communication by using cryptographic keys for authentication, ensuring that only verified entities can interact within the grid. Digital certificates help establish trust between different nodes, preventing unauthorized users from gaining access.
Additionally, biometric authentication, such as fingerprint or facial recognition, can add an extra layer of security. While not always practical in large-scale grid systems, biometric authentication can be useful in restricted environments where high-level security is required.
Securing Data Transmission with Encryption
Grid computing systems rely heavily on data transmission between nodes. If this data is not encrypted, attackers can intercept sensitive information during transit. Secure encryption protocols, such as Transport Layer Security (TLS) and Secure Shell (SSH), help protect data from being accessed by unauthorized parties.
End-to-end encryption ensures that data remains protected throughout its journey across the grid. Even if attackers intercept communications, encrypted data remains unreadable without the proper decryption keys. Using strong encryption algorithms, such as AES-256, can significantly reduce the risk of data leaks.
For additional security, organizations should implement virtual private networks (VPNs) to create secure communication channels. A VPN encrypts all transmitted data, reducing the risk of unauthorized interception, particularly when users access the grid remotely.
Implementing Role-Based Access Control (RBAC)
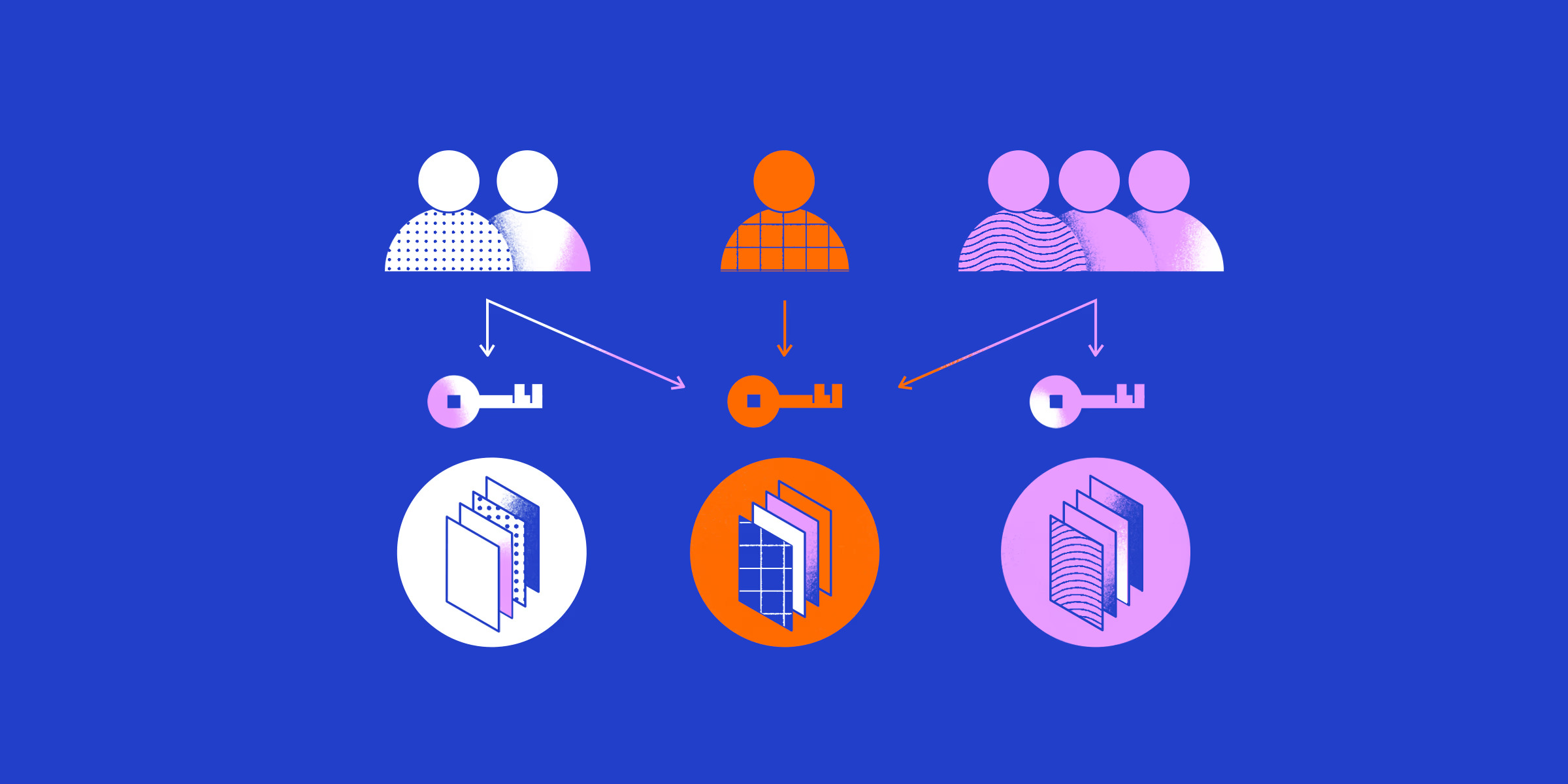
Not all users in a grid computing environment require the same level of access. Role-Based Access Control (RBAC) ensures that users are granted permissions based on their responsibilities. By assigning specific roles, organizations can limit access to sensitive data and computational resources, reducing potential security risks.
RBAC works by categorizing users into different groups, such as administrators, researchers, and external collaborators. Each group has predefined access permissions, ensuring that users can only interact with the components necessary for their tasks. This approach minimizes the risk of accidental data exposure or unauthorized modifications.
Furthermore, dynamic access control policies can be implemented to adjust user privileges based on real-time conditions. For example, if an employee leaves the organization, their access rights should be automatically revoked to prevent lingering security vulnerabilities.
Continuous Monitoring and Intrusion Detection
Preventing unauthorized access requires ongoing vigilance. Continuous monitoring helps identify unusual activity patterns that may indicate a security breach. Intrusion Detection Systems (IDS) and Security Information and Event Management (SIEM) tools can provide real-time alerts when suspicious activity is detected.
Behavioral analytics can further enhance security by identifying anomalies in user behavior. For instance, if a researcher suddenly logs in from an unfamiliar location or attempts to access restricted files, the system can trigger an alert for further investigation.
Periodic security audits also play a critical role in preventing unauthorized access. Regularly reviewing user access logs, network activity, and authentication records helps identify vulnerabilities and take corrective actions before they are exploited.
Implementing Secure Middleware Solutions
Middleware acts as the communication bridge between different components in a grid computing system. If middleware lacks proper security measures, it can become a weak point for unauthorized access. Secure middleware solutions must include authentication, encryption, and access control features to protect data and computing resources.
Some middleware solutions, such as UNICORE and Globus Toolkit, offer built-in security mechanisms that enforce authentication and data integrity. Organizations should choose middleware that aligns with their security requirements and ensures compliance with industry standards.
Regular updates and patches are essential to keep middleware protected against emerging threats. Cybercriminals often exploit outdated software, so keeping systems up to date is a fundamental part of security management.
Protecting Against Insider Threats
While external attackers pose a significant risk, insider threats can be just as dangerous. Employees, researchers, or contractors with legitimate access may misuse their privileges for financial gain or personal motives. Establishing strict policies can help prevent insider-related security breaches.
Access logs should be monitored regularly to track user actions within the grid. If an individual attempts to access restricted resources or downloads excessive amounts of data, security teams should investigate the activity. Implementing least-privilege access policies ensures that users only have access to what they need for their roles.
Security awareness training is also crucial. Educating employees about phishing attacks, social engineering tactics, and password security can help prevent accidental security breaches caused by human error.
Strengthening Endpoint Security
Grid computing often involves users accessing resources from various endpoints, including personal computers, institutional networks, and cloud-based services. If an endpoint is compromised, an attacker can use it as an entry point into the grid system.
Organizations should enforce strict endpoint security policies, such as requiring updated antivirus software, firewalls, and device authentication. Restricting access to approved devices can further minimize security risks.
Using endpoint detection and response (EDR) solutions can help identify potential threats before they spread. These tools monitor endpoint activity, detect suspicious behavior, and provide automated responses to mitigate security incidents.
Building a Resilient Security Strategy
Securing a grid computing system from unauthorized access requires a multi-layered approach. By implementing strong authentication, encryption, continuous monitoring, and strict access controls, organizations can reduce vulnerabilities and maintain the integrity of their distributed computing environments.
As technology advances, so do cyber threats. Staying proactive with regular security updates, employee training, and robust security policies will help prevent unauthorized access and ensure the reliability of grid computing systems.